According to IMB's Cost of a Data Breach Report 2025, the healthcare sector hit a grim milestone recently as the average cost of a data breach surged to nearly million . We are looking at a predatory landscape where ransomware groups target unpatched legacy systems with surgical precision.
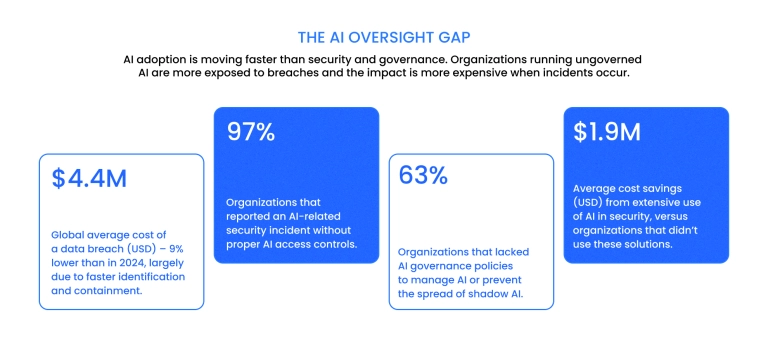
While the Office for Civil Rights (OCR) continues to levy multi-million-dollar fines for "right of access" failures, the real threat to modern medical enterprises is the "silent leak" through unvetted analytics pixels and unsecured APIs. For any provider, the margin for error is gone.
The digital transformation of medicine is no longer optional, but it must be built on a foundation of uncompromising privacy. Navigating HIPAA compliant software development in 2026 requires more than a basic checklist. It demands a shift toward Zero Trust architecture and a "Compliance as Code" mindset where security is baked into every sprint.
Binariks specializes in high-stakes healthcare software development that bridges the gap between rapid innovation and federal regulation. In this guide, we break down the technical barriers to creating HIPAA compliant software that is resilient enough to meet the next generation of cyber threats.
In this article, you will discover:
- The 2026 regulatory shifts regarding the HIPAA Security Rule and mandatory technical safeguards
- How to integrate LLMs and Generative AI into patient portals without violating privacy
- The technical architecture required for modern HIPAA compliant software development
- Strategies for auditing third-party SDKs and tracking pixels to prevent impermissible disclosures
- A comprehensive checklist for HIPAA compliant software deployment and maintenance
Read on to master the complexities of modern healthcare compliance and protect your organization from evolving digital risks.
What is HIPAA compliance?
HIPAA compliance is a legal obligation for any organization that handles Protected Health Information (PHI) to implement specific physical, network, and process security measures.
The core legislation remains the Health Insurance Portability and Accountability Act of 1996. But the 2026 reality is governed by a 'prove it' enforcement model. Regulators no longer accept documentation of intent; they demand evidence of technical enforcement.
Understanding whether your project requires a HIPAA-compliant system starts with identifying your role in the data chain.
Covered entities vs. business associates
The law distinguishes between those who own the data and those who build the tools to manage it:
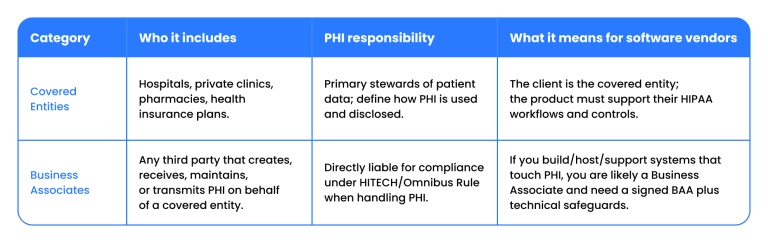
If you are a software vendor, a cloud provider, or an IT consultancy, you are likely a Business Associate. Under the HITECH Act and subsequent Omnibus Rule, you are directly liable for compliance. The HIPAA standard applies to you the moment a single patient identifier, such as a name, email, or IP address, enters your environment. This is why Binariks integrates security from the start when developing telemedicine software solutions or complex EHR platforms.
Determining whether your HIPAA-compliant software is actually up to code depends on three major technical pillars:
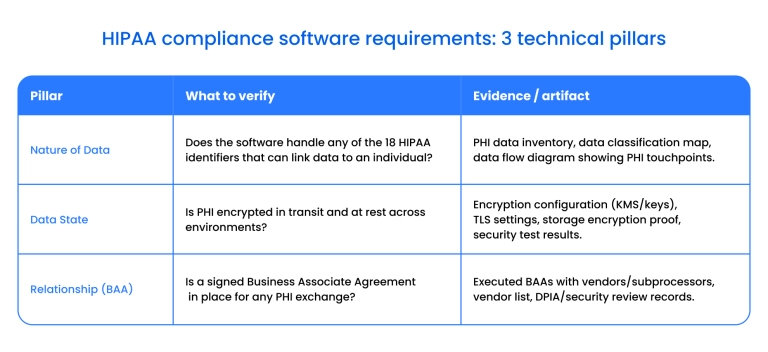
For developers, the goal is to build a system where security is not an add-on but an immutable part of the architecture. Healthcare remains the most targeted industry for unauthorized access, making compliance essential to long-term operational continuity.
Who needs to comply with HIPAA privacy standards?
According to the HHS Cybersecurity Performance Goals , federal oversight has shifted toward a zero-trust mandate, effectively eliminating the leniency once granted to smaller software vendors.
To maintain a compliant environment, teams must now treat encryption and multi-factor authentication as mandatory technical safeguards rather than optional configurations. This shift ensures that applications are resilient enough to meet current federal standards for automated threat detection and rapid incident response.
Adhering to these rules requires a "Security by Design" approach in which privacy and breach notification protocols are integrated directly into your CI/CD pipeline. When building HIPAA-compliant software, every data flow must be mapped to ensure that patient information is accessible only under the "minimum necessary" principle.
For teams engaged in HIPAA software development, this means the product must not only protect data but also provide a verifiable audit trail that holds up under increasingly rigorous federal inspection.
HIPAA compliance software requirements
The baseline for HIPAA compliance for software development is no longer a static goal but a continuous state of technical and administrative readiness. While the Department of Health and Human Services (HHS) outlines broad rules, software that provides even a temporary conduit to Protected Health Information (PHI) must meet specific technical thresholds.
For any team developing a HIPAA-compliant app, these requirements ensure that patient data remains secure from the point of entry to the point of storage.
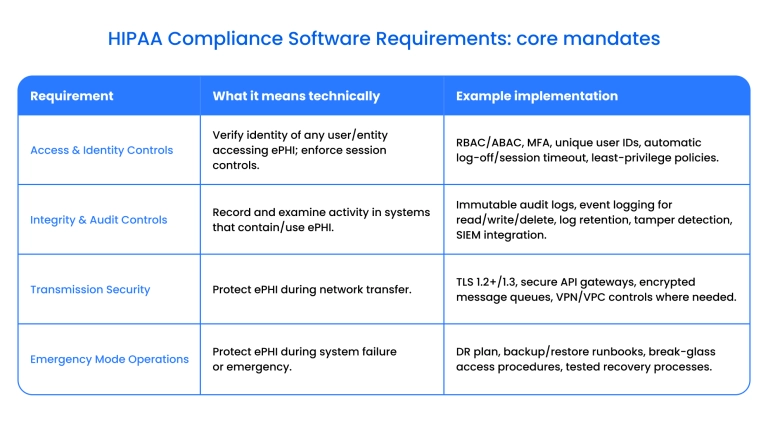
To maintain HIPAA compliance for software vendors, your architecture must satisfy these core mandates:
- Access and identity controls. The system must verify the identity of any person or entity seeking access to ePHI and implement automatic log-off procedures.
- Integrity and audit controls. You must implement hardware, software, and procedural mechanisms that record and examine activity in all systems that contain or use ePHI.
- Transmission security. All data must be encrypted to guard against unauthorized access during EMR/EHR development or when moving through any network.
- Emergency mode operations. Modern HIPAA software requirements mandate that you have established procedures for protecting the security of ePHI during any system failure or emergency.
Any medical software used to store, transmit, or operate on patient identifiers must adhere to these regulations. Failing to integrate these safeguards into your foundational code can result in significant financial penalties and a total loss of user trust.
Want to become HIPAA-compliant?
Learn about best practices of FHIR implementation.

HIPAA checklist for building healthcare software
According to the 2026 HIPAA Security Rule Modernization guidance , federal standards have transitioned from documenting intent to proving technical enforcement. For any team managing HIPAA-compliant development, this means formerly "addressable" safeguards like encryption are now mandatory across all systems.
This shift requires that applications demonstrate real-time resilience through automated asset inventories and enforced multi-factor authentication for every user.
Modern checklists for HIPAA-compliant applications must also address the risks of integrated AI and legacy system vulnerabilities. If your platform utilizes a HIPAA-compliant LLM for patient data, you must implement strict data isolation to prevent unauthorized model training.
By embedding automated audit logs and 72-hour restoration capabilities into your lifecycle, you ensure that HIPAA app development meets the current federal "zero-trust" mandate while utilizing HIPAA-compliant technology.
The technical requirements checklist
- User Authorization. Implement a multi-tiered identity assurance system. This includes knowledge (passwords), inherence (biometrics), and possession (security codes) to ensure only legitimate users access sensitive data.
- Emergency Mode. Define clear procedures for data protection during a crisis. Your plan should include a detailed contact list, a step-by-step execution strategy, and a clear identification of potential hazards acknowledged by all business partners.
- Remediation Plan. Create a security strategy that details best practices for securing patient data. This must identify specific team responsibilities and provide an actionable roadmap for overcoming future security challenges.
- Data Backup. Ensure all ePHI is copied to a reliable, secondary storage system. Use 256-bit AES protocols for encryption and implement automated monitoring to notify staff immediately if a backup fails.
- Proactive Monitoring. Use automated risk detection to examine activity logs and identify suspicious attempts to access the system. The software must also enforce automatic logouts once a user's shift or session is complete.
Navigating these requirements demands a shift from reactive patching to a "Security by Design" philosophy. By focusing on multi-factor identity verification, robust emergency protocols, and encrypted data redundancy, developers can build a foundation that protects both patient privacy and organizational integrity.
Get a HIPAA consulting services from solution architects, BAs, and engineers
How to make your software HIPAA compliant?
Transforming a standard application into a regulated medical product demands a deep integration of administrative and technical controls. According to the Cybersecurity Resource Guide , "regulated entities should not view risk assessment as a one-time, static task but as an ongoing activity."
This directive reinforces that HIPAA software compliance requires continuous technical vigilance and periodic updates to manage the "dynamic environment" of emerging threats and new vulnerabilities.
This means HIPAA-compliant applications must treat security as a core architectural priority, implementing "reasonable and appropriate" measures tailored to their specific technical environment.
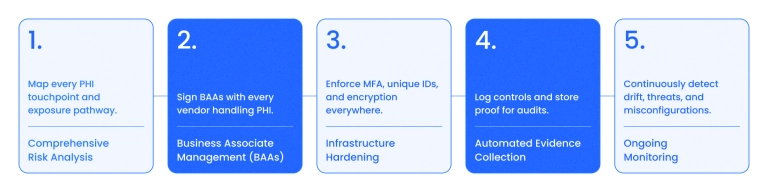
To successfully navigate HIPAA-compliant app development, your team should follow a rigorous implementation roadmap:
- Comprehensive risk analysis. Map every point where Protected Health Information (PHI) is created, received, maintained, or transmitted. This ongoing process identifies conditions under which data could be improperly modified or disclosed without authorization.
- Business associate management. Secure a signed Business Associate Agreement (BAA) with every person or entity (such as cloud providers or subcontractors) that performs functions involving PHI on your behalf. A business associate is legally "liable for their own HIPAA violations".
- Infrastructure hardening. Align your environment with HIPAA compliance software requirements by enforcing technical safeguards. This includes unique user IDs and multi-factor authentication to ensure "person or entity authentication", as well as 256-bit encryption for "transmission security".
- Automated evidence collection. Maintain "written or electronic records" of all assessments and activities required by the Security Rule. This documentation provides the "foundation for a regulated entity's Security Rule compliance efforts" and is essential for federal evaluations.
Achieving compliance is a strategic investment in your product's credibility. By focusing on deep infrastructure hardening, rigorous vendor management, and automated monitoring, you build a resilient foundation that protects patient privacy while allowing your software to scale safely in a regulated market.
HIPAA-compliant software development
Architecture consulting and FHIR implementation for healthcare platform
The regulatory framework for HIPAA software compliance
Understanding the technical obligations of a medical platform requires more than a checklist; it requires understanding the legal pillars that dictate data handling. According to the HHS Cybersecurity Performance Goals , the federal government has identified "Essential Goals" that represent the minimum security floor for all entities, ensuring that the "confidentiality, integrity, and availability" of patient records are technically enforced.
When building a HIPAA-compliant application, you must align your architecture with these primary mandates:
- The Privacy Rule. This establishes a patient's right to control their own data. For HIPAA-compliant applications, this means building features that allow patients to examine, request copies of, and ask for corrections to their health records. Your software must facilitate these rights while ensuring that data use is restricted to the "minimum necessary" to perform a specific task.
- The Security Rule. This is the technical heart of regulated development. It dictates the administrative, physical, and technical safeguards needed to protect electronic PHI (ePHI). Modern standards require that your system prevent unauthorized access through granular identity management and encrypted storage protocols.
- The Breach Notification Rule. This mandate requires that systems have a mechanism for identifying and reporting data exposures. To meet modern HIPAA compliance software requirements, you must implement real-time monitoring and logging so that if a breach occurs, the affected individuals and federal regulators are notified within strict legal timeframes.
By shifting the focus from outdated legacy statutes to the core technical goals outlined by the HHS, developers can build a framework that is both legally compliant and technically sound. This regulatory alignment ensures that your software can adapt to the "flexible and scalable" nature of federal oversight while maintaining the highest standards of patient data protection.
How to build HIPAA-compliant software?
Building a medical application in 2026 requires moving beyond basic functionality to a "Security by Design" architecture. According to the Guide , "the Security Rule is flexible, scalable, and technology-neutral," which means your development lifecycle must be tailored to the specific risks of your environment while maintaining continuous technical vigilance.
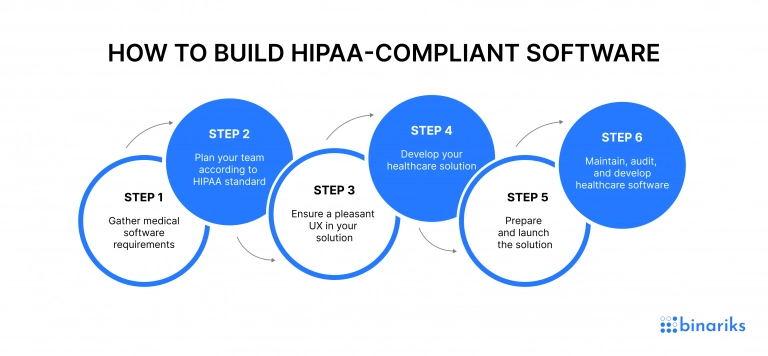
Step 1: Mapping data flows and technical requirements
Before writing code, you must identify every point where Protected Health Information (PHI) enters, resides, or exits the system. This stage involves defining the HIPAA compliance software requirements for data isolation and user roles.
Rather than relying on general goals, establish a "Minimum Necessary" data access policy, ensuring that the software architecture restricts information access to only what is required for a specific clinical or administrative task.
Step 2: Risk-based project planning
Successful HIPAA-compliant software development depends on a formal risk analysis to identify potential vulnerabilities in your proposed tech stack. This planning phase must define the specific technical safeguards — such as automated session timeouts and 256-bit encryption — that will be integrated into the product.
It is also the stage at which you must secure Business Associate Agreements (BAAs) with any third-party service providers, such as cloud hosts or API vendors.
Step 3: Secure UX and UI design
Design in healthcare must balance usability with strict security protocols. In this phase, create user interfaces that enforce "Person or Entity Authentication" without compromising workflow efficiency.
This includes designing intuitive flows for Multi-Factor Authentication (MFA), clear emergency access pathways ("break-glass" procedures), and automatic log-off warnings that prevent unauthorized viewing of screens in shared clinical environments.
Step 4: Secure healthcare software development
During the engineering phase, developers must implement the core technical safeguards required by the Security Rule. This includes building immutable audit logs that record all "Read, Write, and Delete" actions on PHI and ensuring all data in transit utilizes TLS 1.3. For modern interoperability, focus on integrating FHIR (Fast Healthcare Interoperability Resources) standards to ensure data remains secure and structured as it moves between healthcare systems.
Step 5: Pre-launch auditing and risk remediation
Prior to deployment, the software must undergo rigorous penetration testing and a final security assessment.
This stage of the HIPAA compliance checklist requires identifying any remaining security threats and documenting your mitigation strategies. You must verify that your backup and recovery protocols are functional and that all staff involved in the launch are trained on the privacy protocols governing the new system.
Step 6: Continuous maintenance and lifecycle auditing
Post-launch, the focus shifts to "ongoing activity" as mandated by federal guidelines. HIPAA compliance is not a "one-time, static task" but requires continuous monitoring of system activity, regular vulnerability scans, and the periodic application of security patches.
Maintain a defensible audit trail by keeping electronic records of all security assessments and system modifications to prove compliance during any future federal evaluation.
Developing a compliant medical application is a strategic commitment to data integrity. By integrating formal risk management and rigorous technical safeguards into every stage of the lifecycle, development teams can build resilient platforms that satisfy federal auditors while protecting the most sensitive patient information.
Choosing a HIPAA-compliant software development company
To ensure successful HIPAA-compliant software development, your team should include these specialized roles:
- Solution Architect & HIPAA Consultant: Together, they select a HIPAA-compliant technology stack and design a "Security by Design" architecture that ensures data isolation and system resilience.
- Back-End & Front-End Developers: These engineers build the business logic and interfaces, strictly enforcing "Person or Entity Authentication" and encryption for data both at rest and in transit.
- DevOps & QA Engineers: DevOps specialists manage secure CI/CD pipelines and automated monitoring, while QA engineers perform rigorous vulnerability scanning and penetration testing to identify potential leaks before launch.
- Business Analyst & UX Designer: The BA maps complex data flows to meet HIPAA compliance software requirements, while the UX Designer ensures the UI facilitates secure workflows, such as automatic session timeouts and MFA.
- Project Manager: Acts as the compliance anchor, managing the HIPAA compliance checklist for software development, analyzing risks, and ensuring the project stays within its legal and budgetary framework.
Binariks Experience
Binariks offers extensive expertise in engineering HIPAA-compliant applications for global healthcare providers and startups. We navigate the "flexible and scalable" nature of federal regulations to build architectures that are both legally defensible and technically resilient. From modernizing legacy EHRs to launching patient portals, we ensure your product meets the most stringent HIPAA compliance software requirements from the first sprint.
Our portfolio includes multiple cases of providing clients from the healthcare sphere with top-notch HIPAA apps. In particular, Binariks optimized a personalized patient monitoring system . Our dedicated team of cloud specialists used native AWS services to enhance the flow of information and increase the analytical capacities of the client's software. We also paid attention to the security of patients' identifiable data stored on a platform to deliver a HIPAA-compliant product meeting all client's expectations.
Binariks helped an American provider of healthcare technologies in the maintenance of two applications dealing with healthcare plans. Our developers also used Swift and React Native to create two new HIPAA-compliant mobile apps for the client. The products deal with patients' identifiable data, which has made our developers focus on delivering secure products that meet all HIPAA requirements.
We understand how to fulfill HIPAA software standards and design medical solutions with secured patient portals to manage their electronic health information to patients and other authorized stakeholders.
Check our portfolio to get more information on how to develop HIPAA-compliant apps.
Conclusion
Violation of HIPAA regulations can lead to significant fines and severe reputational damage. To remain compliant, entities must establish rigorous technical safeguards and choose partners capable of navigating this environment.
With extensive experience in HIPAA-compliant applications, Binariks provides the technical expertise required for secure medical software. Whether you are building from scratch or aligning with HIPAA compliance software requirements, we ensure your product is both legally sound and technically resilient.
Contact us today to discuss your project; in healthcare, choosing a credible expert is your most important security control.
FAQ
Share

